SPOOFING AN AUTHENTICATION COOKIE
- Layout for this exercise:

1 - Authentication cookies
- Authentication cookies are the most common method used by web servers to know whether the user is logged in or not, and which account they are logged in with.
https://en.wikipedia.org/wiki/HTTP_cookie
- Without such a mechanism, the site would not know whether to send a page containing sensitive information, or require the user to authenticate themselves by logging in.
- The security of an authentication cookie generally depends on the security of the issuing website and the user's web browser, and on whether the cookie data is encrypted.
- Security vulnerabilities may allow a cookie's data to be read by a hacker, used to gain access to user data, or used to gain access (with the user's credentials) to the website to which the cookie belongs.
- In this exercise the OWASP WebGoat v5.4 will be used for the purpose of exemplifying the spoofing of an authentication cookie:

2 - Session Management Flaws
- Going to Session Management Flaws -> Spoof an Authentication Cookie:

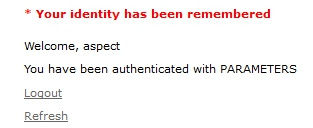
- The scenario consists of a login web form that works correctly for two different username/password cases, for instance signing in with webgoat/webgoat and aspect/aspect the authentication is ok:



- However, the challenge is to achieve a successful authentication bypass for the user alice, what at first is rejected by the login process:


3 - Tampering the authentication process
- With the purpose of retrieving authentication cookies for webgoat/webgoat and aspect/aspect let's use the Tamper Data add-on of the browser Firefox:

- Starting the tamper:

- Now, let's sign in with webgoat/webgoat:

- Tampering:

- Copying the cookie:

- Storing the authentication cookie for further study:

- Same thing for aspect/aspect:




- As a result of the tampering, now we have two authentication cookies, one for webgoat/webgoat and the other one for aspect/aspect:

- Comparing the two cookies it is clear that both start by 65432 and end up with two different strings: ubphcfx and udfqtb
4 - Decoding/encoding the cookies
- Going to:
yehg.net/encoding
- Entering the string ubphcfx and reversing:



- Decoding with Char-- (shifting down one character):

- The result is the expected webgoat:

- Same process with the authentication cookie udfqtb obtained for aspect/aspect:

- So now what we can do is to follow the reverse method with alice in order to achieve a similar string to build a new authentication cookie:

- Reversing and encoding with Char++ (shifting up one character):



- The result is:

- Actually the encoding process is very simple, consisting of just reversing plus shifting one character:
wegboat -> taogbew -> ubphcfx
aspect -> tcepsa -> udfqtb
alice -> ecila -> fdjmb
- To build alice's cookie the string fdjmb is prepended to 65432 in this way:

5 - Launching the cookie spoofing attack
- Now, let's tamper again an authentication session for webgoat/webgoat:



- At this moment, let's copy alice's crafted cookie and paste it into the cookie field:


- Clicking OK:

- Finally the attack is successful and the spoofed user alice becomes authenticated:
